News
the Excellence of Jason Dozier: University of Arizona

The Academic Trailblazer
Individuals who stand out in the ever-changing world of higher education by their significant contributions are worthy of recognition. One such eminent figure is Jason Dozier of the prestigious University of Arizona. Let’s look into his educational background and achievements.
A Glimpse into Jason Dozier’s Journey
The name Jason Dozier is synonymous with academic achievement and originality. He has left an indelible impression on the intellectual fabric of the jason dozier university of arizona
Academic Prowess
Dozier’s academic career is evidence of his diligence and intelligence. His wide range of expertise has not only benefited his own learning, but also inspired others around him. Nothing short of astounding, his contributions to [insert relevant disciplines here] have been.
Research Wizardry
When discussing Jason Dozier, it is impossible to gloss over his prodigious research skills. His studies have expanded the bounds of knowledge, making important contributions to the academic world. He has received widespread respect for his work on [insert research areas here].
Teaching with a Difference
Dozier is not just an excellent scholar, but also a superb professor. His approach to the classroom is novel and highly efficient. His students routinely attest to having life-changing educational experiences while in his class.
Community Engagement
The influence of Jason Dozier is not limited to the classroom. His involvement in charitable work and social concerns is evidence of his desire to improve society. He’s been quite involved in [insert variety of local activities or social problems here].
Supporting a Vision
As we follow Jason Dozier’s story at the University of Arizona, we hope you’ll join us in encouraging him to publish even more of his free writing prompts online. With your help, he can keep doing important research in the academic world.
Conclusion
Jason Dozier is a bright star in the world of higher education. Academic excellence, innovative study, and a dedication to the greater good characterize his time at the University of Arizona. You can help the world and increase human understanding by backing his efforts. Academic excellence is often associated with the name Jason Dozier.
Business
Understanding the Importance of an IOC (Indicator of Compromise)

Introduction
In today’s digitally connected world, cybersecurity stands as a paramount concern for individuals, businesses, and organizations alike. Among the many tools and concepts employed to bolster cybersecurity, the Indicator of Compromise (IOC) emerges as a crucial element. Understanding what an IOC is and its significance is pivotal in safeguarding digital assets and preventing potential cyber threats.
What is an IOC?
An Indicator of Compromise (IOC) refers to any evidence or abnormality observed in a system or network that potentially indicates a cybersecurity breach or an ongoing threat. These indicators vary in nature, ranging from file hashes, IP addresses, suspicious network traffic, to unusual system behavior or unauthorized login attempts.
Types of IOCs
- Hash-based IOCs: These involve unique identifiers generated using algorithms like MD5, SHA-1, or SHA-256, representing a specific file or piece of malware.
- File-based IOCs: Signature-based indicators identifying specific files or components known to be malicious.
- Behavioral IOCs: Abnormalities in system behavior, such as unexpected network traffic patterns or unauthorized access attempts.
- Artifact-based IOCs: Information left behind by attackers during an intrusion, such as logs or system changes.
Importance of IOC in Cybersecurity
Early Detection
One of the primary advantages of utilizing IOCs is their role in early threat detection. By identifying these indicators promptly, security teams can respond swiftly, mitigating potential damage or data breaches before they escalate.
Incident Response and Forensics
IOCs serve as vital breadcrumbs during incident response and forensic analysis. They aid in tracing the origin and scope of an attack, allowing organizations to understand the attack methodology and fortify defenses against similar threats in the future.
Proactive Defense
Employing IOCs enables organizations to adopt a proactive approach to cybersecurity. Continuously monitoring and updating IOCs bolsters security measures, preventing known threats and vulnerabilities from exploiting systems.
Creating and Utilizing IOCs
Collection and Aggregation
Security professionals gather IOCs from various sources, including threat intelligence feeds, security advisories, malware analysis reports, and internal monitoring tools. These indicators are then aggregated and categorized for easier analysis and implementation.
IOC Implementation
Continuous Updating
Cyber threats evolve rapidly, rendering older IOCs obsolete. Regular updates and continuous monitoring are crucial to maintaining an effective IOC strategy. Security teams must stay vigilant, ensuring that the IOCs are updated to detect emerging threats.
Challenges and Limitations
False Positives
One of the challenges with IOCs is the potential for false positives, where legitimate activities or benign elements trigger alarms, leading to unnecessary investigations or disruptions.
Evolving Threat Landscape
Cyber threats continuously evolve, employing sophisticated techniques to bypass traditional security measures. Keeping up with these changes and updating IOCs accordingly is a perpetual challenge.
Lack of Standardization
The absence of standardized IOC formats and protocols can hinder interoperability between different security systems and tools, complicating the sharing and utilization of IOCs across platforms.
Conclusion
In conclusion, the Indicator of Compromise (IOC) serves as a cornerstone in modern cybersecurity practices. Its role in early threat detection, incident response, and proactive defense is indispensable. However, to harness its full potential, organizations must address challenges such as false positives, evolving threats, and standardization issues.
FAQS:
News
Unveiling the Recent Teacher Arrests in Florida

Introduction:
The Incidents:
Nature of Offenses:
Legal Actions Taken:
Impact on Education:
Community Reaction:
Trust and Safety Concerns:
Reflection on Policies:
Scrutiny on Hiring Protocols:
Educator Accountability:
Conclusion:
News
Breaking News: Updates and Developments at CVS
Introduction:
-

 Technology7 months ago
Technology7 months agoKooraLive English: Guide to Live Sports Streaming
-

 Technology7 months ago
Technology7 months agoSSIS 816 Revolutionizing Data Integration
-
 Health7 months ago
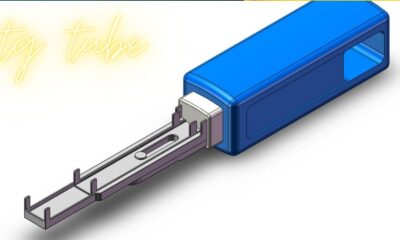
Health7 months agoOptimizing Health: The Comprehensive Guide to TG Tubes
-

 Lifestyle6 months ago
Lifestyle6 months agothe Charm of Villages: Decoding the Loofa Code
-

 Entertainment6 months ago
Entertainment6 months agothe Mystery: packgod face reveal
-

 Business4 months ago
Business4 months agoSimplifying Work Life: NetchexOnline Employee Login
-

 Technology7 months ago
Technology7 months agoThe Power of Innocams
-

 Entertainment4 months ago
Entertainment4 months agoExploring the Marvels of Jable.tv: A Comprehensive Guide to Streaming Excellence